Most people think that APT attackers do penetrate the network by using unique, near-magical recipes based on advanced skills, computer wizardry and a couple of zero day vulnerabilities if not more. This feeling has been relayed and amplified by most media, which seizes every opportunity to increase their readership and their ad-based revenue. In most cases however, such feelings are totally wrong.
APT attackers are like any other skilled professional: they need to be efficient, effective and their operation has to be cost-effective and undetected as long as possible.
Imagine yourself in the role of a real-life thief. You are about to penetrate a house in which you want to steal something. Would you immediately try to break a window glass, or break the front door? Wouldn’t you first check if there is no open window? Maybe the front door is even left open? Of course you would try. It makes complete sense. Why would an attacker in the virtual world behave any differently?
This is what this blog post is about. It might surprise you, but reality is often simpler than what we might think. My goal here is to try to definitely change your opinion on APT attackers by the end of this blog post.
Let’s start with the most common technique used by attackers to penetrate their target’s network: a simple e-mail.
Phishing & Spear Phishing
Phishing describes a technique in which an attacker sends e-mails to people, in the hope that these recipients will answer positively to the e-mail.
The most common phishing attempts do usually have a financial goal: the attacker sends an e-mail which looks like it comes from a legitimate banking company, with a clickable link. The e-mail uses social engineering content to entice the user to click on the link. It brings the user to a fake website, which is a copy of the legitimate banking company’s website, and invites the user to enter their banking account credentials or credit card information. This data is valuable to the attacker as they can use it to steal money from their victims’ bank accounts.
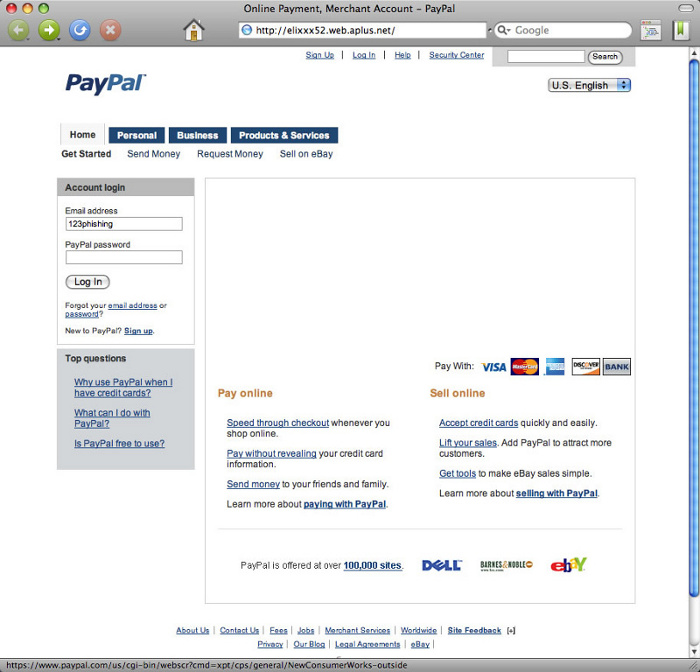
Fake Paypal website – notice the URL of the web page …
Phishing e-mails are generally built by cybercriminals known as “phishers” and sent to several hundreds or thousands of people on the Internet, chosen randomly or selected from a stolen e-mail list (It is very easy to find cybercriminals who sells such lists on underground forums).
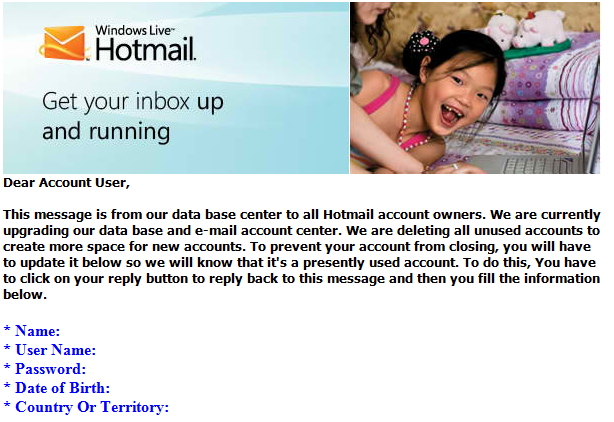
There are at least two other phishing variants. The first one consists of sending e-mails spoofing a legitimate company’s template and asking directly the victims to reply with their credit card numbers or other types of sensitive data. This method is easier to use for attackers because they don’t need to build a fake website. On the other hand, its effectiveness is rather low because people tend to be cautious when asked to send their credentials in “reply” to an e-mail.
Here follows such an e-mail example, which asks users to send over their Hotmail credentials to fraudsters :
The second phishing variant consists of sending an e-mail containing an attached document, which is a Trojan horse. The recipient is enticed into opening the attached document, which is often an executable file disguised as a Microsoft Office document or a PDF file, or an archive file containing a malware binary. It could also be a real PDF file which exploits a software vulnerability and silently installs a Trojan horse that will steal information from the infected computer, generally banking credentials and credit card numbers that the victim use on online payment platforms.
Different social engineering schemes are used to entice the user to open the attached file. Some are very naive while others are very effective and clever. Money is one of the most powerful ways to have people open attached files. For example, some phishers send emails that appear to be sent by the local tax department . These emails often state that there is a problem with the latest payment and that the victim should check the attached document. Some others mention a problem in the tax department, which took too much money and offers to pay back the victim, who just needs to check the document… Possibilities are endless; as soon as the victim clicks on the booby-trapped attachment using a vulnerable environment, the attacker gains a foothold into the target network.
Phishing campaigns are generally massive. Each campaign sends between few hundred e-mails to hundreds of thousands e-mails. It might sound very time consuming and tricky but it is not: attackers can rent spamming botnets . Spamming services have different levels of quality, depending on the e-mail database they use mostly. In the Russian cybercrime underground, it takes between 10 and 500 dollars to send a million e-mails.
Spear phishing can be described as targeted phishing. In a spear phishing scheme, attackers send very few e-mails. In fact, they can even send just a single e-mail. The trick is to target the right victim. There are roughly two kinds of spear phishing in the wild. We can call them “mass spear phishing” and “traditional spear phishing”.
Mass spear phishing
This is a mixture between phishing and spear phishing. In a mass spear phishing campaign, cybercriminals send a huge number of e-mails to selected targets. The selection can be done using various parameters. It could be very basic (just sending e-mails to women, or only to people from one country for example), or a bit more complex, based on professional activities, personal preferences or psychology.
As a more complex example, imagine a person (let’s call this person Thibaud), living in Paris, whose passion is collecting and buying old electric guitars (or just anything else). What are the odds for Thibaud to open a usual phishing e-mail which spoofs the identity of a banking company? Very limited. Now what are the odds for Thibaud to open an e-mail which title would be “Limited offer – Electric guitars for sale in Paris” and which content would show a nice old electric guitar with a little “click here to see more” link? Thibaud would probably click, even if not interested at that time, just to satisfy his curiosity. The attackers used two powerful triggers in this case: first they wrote about the main passion of this person. Then, they mention the town in which he lives. Thibaud is very likely to become a victim very soon; the “click here for more” link will lead the browser to malware infection.
You might wonder how this could happen in real life. How would a distant attacker, not even located in your country (and maybe not speaking your language), know your tastes and passions or your physical location ?
The answer is located in the Internet, as often. In our previous case, the guitar addict was probably registered on one or several forums, in order to exchange information with other guitar collectors. Now what do forums generally ask for when you register? They want your name, maybe your age, your town and country, your e-mail address, and might even ask for more information about you and your passion, which most of the time you fill without second thoughts. This information stays private to the forum, but what happens if it gets hacked? One of the first steps any attacker does after compromising a forum is to dump its user database completely. Some attackers do collect these databases “for glory”, keeping it as a trophy, but some others do use it for mass spear phishing or to sell it in the underground economy of cybercrime.
Now can you imagine the click success rate for cybercriminals sending targeted content to whole communities ? The impact is huge. Yet APT attackers rarely send mass spear phishing e-mail to infect targets. They rather aim for very few e-mail addresses.
Traditional spear phishing
What we call “traditional spear phishing” can be defined as a phishing e-mail sent to a very few people,sometimes to a single person, with content appropriate to the e-mail receiver.
Remember the stage we focus on in the APT kill chain. The reconnaissance phase is over and it is time for the APT attacker to penetrate the company’s network.
In most APT attacks, the compromise of the network starts with one or very few spear phishing e-mail sent to employees. APT attackers prefer this method for several reasons:
- Spear phishing has an open rate of 70%, while it drops to 3% for mass spam e-mails.
- When the attacker is in a hurry, it doesn’t take them long to find a valid e-mail address to which a spear phishing e-mail can be sent.
- It is very easy to do. There is no need for advanced technics here. The only thing the attacker has to take care about is to hide the IP address of the machine sending the e-mail. They can send it from a compromised network, from proxies, from a public Wi-Fi access anywhere; there are many possibilities here to be anonymous.
- As a first entry in the target’s network, attacking from the outside by exploiting server vulnerabilities needs a lot more technical skills and could trigger some alarms on the victim side, if not done the right way.
- Spear phishing usually bypasses e-mail filtering tools. Since the e-mail is probably sent from an unknown IP address (not blacklisted) and sent to very few people, it passes filtering tool.
- Spear phishing will raise no alert. A mass spear phishing campaign could easily be detected on the mail server. Usually, alarms are ringing when suddenly hundreds of e-mails are sent to different people in the company, especially if they come from the same IP address or have the same subject.
- It is very easy to forge an e-mail, in order to make it look like it comes from one colleague, even when you’re outside of the company’s network. There are free tools on Internet to help you with that: the “from” field in an e-mail can be changed.
There are only two potential problems here for the attacker: the first one is that the mail server receiving the e-mail might reject if it has good security parameters. The second problem happens if the receiver replies to a fake address. In that case, the target will know there’s something wrong because they will get an error from the mail server, or an alert can be raised because a real person whose e-mail address has been spoofed receives the answer. To solve that problem, the attacker could use a different “reply to” field, yet that could raise suspicion for the receiver of the e-mail. Another technic for the attacker is to create an e-mail address just for the attack, with a name close to the legitimate one. As an example, let’s say a company called abcdesecurity uses e-mail addresses at abcdesecurity.com. What if the attacker registers a domain name abcdesecur1ty.com and uses it for e-mail address? Will the user immediately notice? Probably not. Even an e-mail like john.doe.abcdesecurity.com@gmail.com might work with some persons unaware of computer security.
According to Trend Micro in November 2012, 91% of APT uses spear phishing e-mails.
These e-mails are generally sent to people without key roles in the company, yet there might be exceptions where APT attackers go directly for the high profiles in the company or project managers, supposed to have access to a lot of resources. It mostly depends on what information the attackers want. They are usually looking for documents about secret projects or highly sensitive intellectual property. Reading the CEO’s emails can be very interesting, but rather for sensitive commercial information or confidential e-mail exchanges with other high profiles people, inside or outside the company. Usually, high profiles are not using e-mail to send or receive confidential PDF files which are more interesting for some attackers.
An example amongst many others might be the APT which impacted RSA in 2011. RSA reports that “The attacker in this case sent two different phishing emails over a two-day period. The two emails were sent to two small groups of employees; you wouldn’t consider these users particularly high profile or high value targets.”
Spear phishing content
Knowing employee’s email addresses is one point. But what is the content of these targeted e-mails? What trigger does the attacker use to entice these persons to open an attachment or click on a link?
The APT attackers need to score. They send very few e-mails, and there has got to be at least one person falling in the trap. They also have to avoid being detected, so the e-mail should not raise any eyebrow from the target user when he receives it and opens it.
Therefore, the e-mail uses target-relevant content. If a person in the Human Resources Department is chosen as a target, the e-mail has got to contain information relevant for the HR employee, like a curriculum vitae or such.
There are many examples of such spear phishing content in APT reports from different computer security companies.
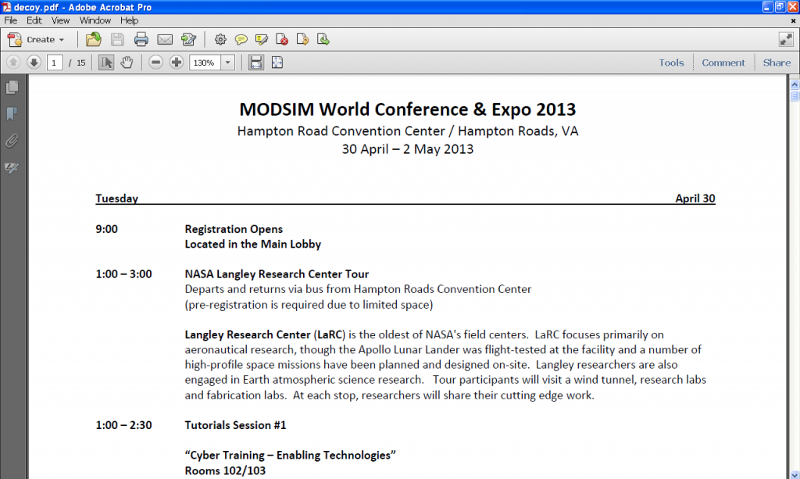
One good example here is a conference agenda for MODSIM 2013, a modeling and simulation event, which is very interesting for people in Defense, Healthcare/Medicine, Engineering & Applied Science, Information Assurance & Cyberwarfare, Cross-Cutting Applications in M&S, Education/Workforce Development, Transportation, and Manufacturing industries.
This document was found by Cybersquared on a server used in an APT attack. It might have been used as a decoy document that the attackers would send to targets in these sectors of activities, to infect them with a malware.
Advice against spear phishing
what should be considered suspicious when a “supposed” colleague sends you an e-mail?
* The use of unexpected sentences. Is your colleague usually familiar when he e-mails you and did you just receive a very formal e-mail from him?
* The signature of the e-mail. Does your colleague always end his e-mails with “Greetings” or such sentence, and it is missing or different? Does your colleague have a corporate signature at the end of every e-mail and it is missing?
* The topic of the e-mail. Would your colleague really e-mail you for that? Wouldn’t he rather give you a phone call?
* Your feeling about it. Does it sound like the only goal of this e-mail is to make you click somewhere or open an attachment?
In case of doubt, you should try to call the person, ask if he really sent you that e-mail. If you do not want to call and prefer e-mailing, send a new e-mail to his legitimate address. Do not reply to the suspicious e-mail, since it could be sent to the attacker.
Social Networks exploitation
In March 2013, Ryan O’Horo, a managing security consultant, used social engineering techniques to gain access to a “high-profile company with tens of thousands of employees”.
This very interesting example shows us what can be done easily for an attacker on social networks. The social network of choice for APT attackers is LinkedIn. It is the biggest professional network worldwide, and nearly every company of a certain size has employees registered there.
But let’s get back to the facts. First, Ryan O’Horo created a realistic fake profile of an employee of the company he was targeting. Of course, all information on LinkedIn is declarative; there is no check on it. It only takes minutes to create such a profile. Ryan then sent 300 LinkedIn invitations to employees of that company. 66 of these people answered positively to the request, without any question. After that, he joined a LinkedIn group belonging to the company, successfully once again, without any verification on him, and had access to approximately 1000 employee’s profiles he could reach.
There, he spread a clickable link, which got 87 clicks in two days, with 40% of it coming from the internal network of the company. He got caught 3 days later, but what would have been the situation if he would have been a real attacker? Multiple malware infections on several hosts from the company, and plenty of time to launch other attacks and install other backdoors anywhere on the network.
This example shows one weakness of the user’s habits on this social network. Yet APT attackers do not need to go to such LinkedIn group. They only need an account, and start browsing profiles, as explained in the reconnaissance phase. Then, they can reach the interesting profiles, and send them malware.
There are more interesting social networks for cybercriminals. Facebook might sound far from the corporate world, but is it really? People speak on it about their work. They do often with their real names. They set a location (at least a town) to show where they live. If their profile is public, you can learn much about them. They might speak of secret projects, and probably a lot about their hobbies and passions. This can once again be used to trick them with an infecting spear phishing e-mail. They could also be infected directly via Facebook.
These users are probably checking their social networks from home, at least for Facebook, which is generally blocked by the corporate filtering solution.
But what happens if an attacker compromises a home computer from a targeted employee? Does the employee store some corporate information there because he wants to work on it? Does he store information of value for the attacker? Does he have a VPN access to the company? Or a plain-text file with all his corporate passwords? Maybe he brings his work computer home and connects it to the Internet without any filtering ?
If the attackers steal the credentials and certificates from the user, the game is over; the attacker has a way to access the corporate network. They will of course also install a backdoor on that corporate laptop, which will be a good access point when it will be connected from the work place. Any social network can be used by APT attackers to learn more about people and to infect them successfully with a Trojan horse, or a remote administration tool, or any kind of backdoor.
Watering hole infections
Fraudsters interested in infecting as much computers as possible (usually to create big spamming botnet or steal banking credentials or credit card numbers) can use the method we just spoke about: they can infect a famous website, which has thousands of visitors every day, to spread malware and infect more people.
One of the first huge examples has been revealed in the beginning of the year 2007, when the official website of the Dolphins Stadium was hacked, short before the Super Bowl final. One single line of code was added by the attackers to the front page of the website, leading to a script trying to exploit two known vulnerabilities to install a Trojan horse. This method allowed the attackers to infect loads of computers. Yet this attack was not targeted, the goal was probably to get easy money by stealing banking credentials and credit card numbers to the infected users.
Now imagine what happens when attackers do compromise a very specific website, which is only infected by a certain category of people? This is what we call a “watering hole attack”. The term was created by RSA and is now used in a standard way to describe such attacks.
Remember, attackers have a very good knowledge of their targets after the reconnaissance phase. In particular, they probably know who the main suppliers of their target are. The next step to build a watering hole attack would be to compromise the website of such a supplier, in order to infect every visitor of that website. The method has one major drawback: it will also infect third parties who visit the website. Attackers have developed ways to avoid this. If their reconnaissance phase has been done seriously, they already know all IP ranges used by the target company. It just takes few lines of code in the infecting script to only compromise visitors coming from the target IP ranges.
A scenario even worse can be used: attackers can infect everyone, and then sort targets by IP addresses. They could infect several corporate companies working in the same industry, with a single watering hole website. This is probably the fastest way to compromise several targets in one move. Multiple APT against every interesting target will be the next move, if the group of attackers is big enough to handle it.
One hit for multiple targets – owning global services providers
Watering hole infections, as seen in previous paragraph, are a good way of infecting loads of interesting targets visiting one particular website, which is usually highly specific and therefore only accessed by potential targets.
Another variant consists of attacking and dumping databases of global services providers. One famous case impacted Epsilon, a large e-mail service provider worldwide. This provider had been breached and leaked thousands of e-mail addresses and names which could be used as spear-phishing material to compromise more companies.
Email services providers are a target of interest for attackers to get information and ways to infect more targets, but so are hosting providers and more generally every important service provider.
Not only can such attacks provide information about potential targets, but also be a direct way of attacking: who would expect a legitimate email from a trusted service provider to spread malware and infect systems?
One might wonder who he can trust, if even their partners might be used to stab them in their back. The answer would be that you should trust your partners to an acceptable level, but not trust them blindly. Do not whitelist everything coming from your partners.
Direct attacks
This is the most straightforward scenario for an initial compromise. In this kind of compromise, the attackers do target servers from the target which are connected to Internet. The web servers are the most targeted servers here. In the case of an APT attack, there are other targeted servers: DNS servers, e-mail servers, or just any server connected to Internet. Once the attackers have found a vulnerability, they launch their attack and compromise the servers, to obtain more information or hop inside the network ,explore further, and install backdoors.
Shell Crew for example is a known actor appreciating this kind of approach.
Physical access
Some decades ago, corporate companies were fewer on Internet. As it was not so widespread, other technics were used in the espionage world. Thrashing was an excellent choice (collecting contents of corporate thrashcans to get information), and getting a physical access to parts of the buildings of companies was also a serious matter.
Nowadays, corporate networks are nearly all connected to the Internet, which provides a lot of possibilities for a willing attacker. We have seen several ways to infect computers inside the target’s network, and the next phases, which are to strengthen the accesses and steal information, will be as easy. Everything is done remotely, and it works very well this way.
This makes “physical espionage” almost useless, yet it still can happen.
Conclusion
Although there are some exceptions like the Elderwood platform, APT attackers do not often use 0day exploits. There is no need for most attackers to find or buy such 0day exploits impacting world-spread applications or the operating system itself, because most companies have bad patch management policies which make them very vulnerable.
These attackers intensely use spear phishing as a first point of entry in the corporate network, by compromising machines of average employees or of high profiles in the company.
The cases witnessed worldwide shows that the attackers generally have a good knowledge of their target. While some attackers might be less effective in their profiling of the target, most do know the targeted companies enough to build very convincing spear phishing content, which is opened by the unsuspecting receiver of the infecting e-mail. Attackers do sometimes even use official documents they stole from another victim to entice the person into opening the attached file which will infect him.
Our next blog post on APT will be about malware and exploits used in APT. Once again, we want to provide general information and raise awareness. More technical blog posts will be published after this serie of posts about APT attacks.


