“There are only two types of companies: those that have been hacked and those that will be hacked.”
Robert S. Mueller III, former Director of the FBI
In today’s world, many organisations understand that they must invest budget and resources to reduce risk and the potential business impact of a cyber attack.
Yet no so many organisations are fully aware of how their cyber resilience stacks up against their adversaries – and all too often this question is first answered once it’s too late and an incident has already occurred.
To gain insights into how strong the security measures that you already have in place are, Airbus CyberSecurity offers Red Team Exercises with an assumed breach approach.
The problem
From a threat vector side, organisations may have dozens of entry points that could allow them to compromise the company’s systems. This is because it is almost impossible to have a “100% secure” environment.
In order to get an informed overview regarding an organisation’s security level, there are a number of offensive security proposals that can be utilised, including:
- Vulnerability Assessments
- Penetration Tests
- Red Team Exercises
- Adversary Emulation
- Purple Team Exercises (Red and Blue teams working together)
While Vulnerability Assessments and Penetration Tests are extremely useful tools in specific use cases, they mainly focus on technology and are often limited to a particular scope. The outputs of these types of assessments are insights into the (current) exploitability of a system – using identified vulnerabilities.
In contrast, Red Team and Purple Team exercises provide holistic assessments of the entire cyber kill chain – including not just technology, but also people and processes.
This also addresses questions around “if”, “when” and “how” an organisation is able to detect and defend against ongoing attacks.
The solution
Airbus CyberSecurity offers Red Team exercises. Our approach is influenced by famous Red Team frameworks like TIBER-EU and MITRE Adversary Emulations.
The approach consists of the following phases:
- Threat Intelligence
- Preparation Phase
- Execution Phase
- Closure Phase
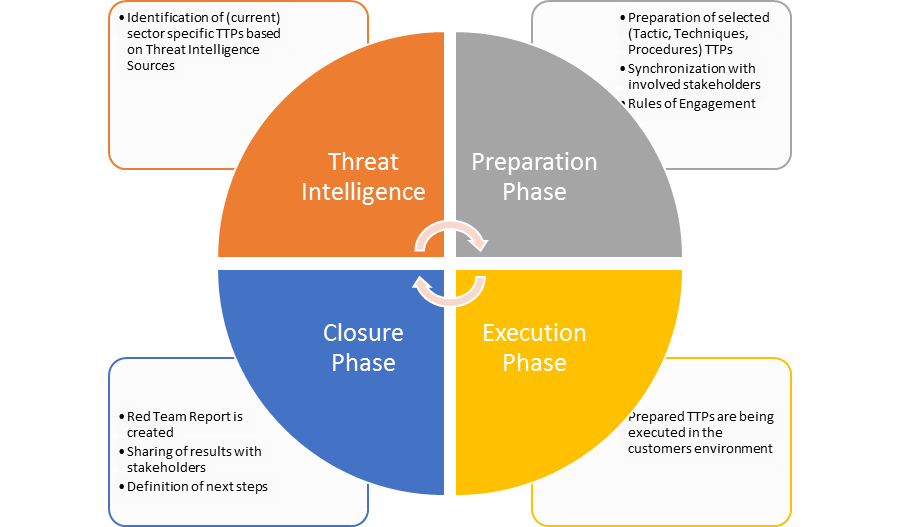
The Red Team approach of this proposal uses an “assumed breach” as a start point, with a compromised (regular) user client. The team will then attempt to gain deeper network access by compromising other systems.
To access the provided user client, we offer a number of options, which will be discussed and aligned in the kick-off meeting with the customer.
Deliverables
Following the Red Team exercise, the customer will receive a detailed report, which contains the following elements:
- Executive Summary
- Applied Methodology
- Executed TTPs (Tactics, Techniques, Procedures)
- Analysis and Response
- Metrics:
- Time of Execution
- Time of Detection
- Time of Response
- Conclusion and Next Steps
A closure meeting will also take place, where the Airbus CyberSecurity team will present findings and recommendations to the customer.
Interested in learning more? Contact your Key Account Manager.


